
Pavan Thatha, head of bot management solutions, Radware
Cybercriminals are siphoning the personal information of millions of shoppers. Dubbed “AuthBots” because of their persistent attempts at cracking authentication, this botnet group targets ecommerce firms with large-scale credential stuffing and cracking attacks to take over user accounts.
Using an army of bots run from fraudulently acquired IP addresses, the AuthBots made nearly 100 million hits on login pages of ecommerce businesses during the first three quarters of 2019. All ecommerce firms with mandatory login are targeted by AuthBots.
Security researchers from Radware first noticed similar bot fingerprints across many ecommerce domains in late 2018 and started tracking the botnets. The following report illustrates sophistication and rapid evolution of AuthBots and its damaging effect on ecommerce ecosystem.
The analysis is possibly only a fraction of AuthBot’s true impact. The total ongoing impact of AuthBots on the ecommerce ecosystem may be larger, since Radware researchers’ analysis is limited to the domains monitored by us.
A Snapshot of AuthBot Operation
Observed First: Late 2018
Volume: Nearly 2.3 billion hits on login pages of ecommerce firms during Q1 – Q3 2019
Operation Infrastructure: 52 million of AuthBot hits originated from 10 prominent data centers/public clouds
Operation method: (1) Credential stuffing attacks using stolen/purchased credentials (2) Credential cracking or brute force attack
Advanced Techniques to Evade Detection
- Manipulation of geo-location and IP addresses through proxy servers
- Over half of AuthBothits originated from data centers/public cloud services
- Most of IPs used by AuthBotsare in the U.S.
- Distributed over hundreds of randomly assigned IP addresses & residential proxies
- Human-like keystrokes and mouse movements
- Use of machine learning and Robotic Process Automation (RPA) to help bots work as standalone software module
- Daisy-chained to manage through one centralized server
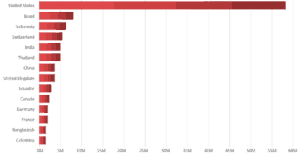
Origin of Autobots: Top countries
Business Impact
- From Q1 – Q3 2019, a significant percentage of traffic was AuthBotson targeted ecommerce firms’ login page.
- Once an AuthBotoperation is successful, PIIs [personally identifiable information] and payment card details of compromised accounts are stolen.
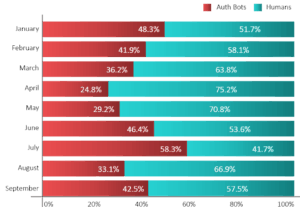
Business impact of AuthBots, by month
Recommendations to Prevent AuthBot Attacks
AuthBots are predominantly fourth-generation bad bots. These bots can connect through thousands of IPs based in different geographies and mimic human behavior. Detecting and mitigating AuthBots requires advanced technology such as one from a dedicated bot management solution provider. However, following are a couple of measures that ecommerce firms can implement to restrain AuthBot activity until they deploy a dedicated solution.
1. Block Bad Bot Harboring Public Clouds/Data Centers
A significant percentage of AuthBots come from public cloud/data centers. Organizations can block suspected data centers/public cloud services. However, blocking all the traffic coming from data centers or ISPs without considering the user behavior can cause false positives.
For example, a significant number of users from commercial organizations that use secure web gateways (SWGs) to filter user-initiated traffic also come from data centers, as these SWGs are hosted on data centers. Blocking data center traffic without considering domain-specific user behavior can cause false positives in such events.
2. Monitor Failed Login Attempts and Sudden Spikes in Traffic
AuthBots perform credential stuffing and credential cracking attacks on login pages. Since such approaches involve trying different credentials or a different combination of user IDs and passwords, it increases the number of failed login attempts. The presence of AuthBots on your website suddenly increases the traffic.
Monitoring failed login attempts and a sudden spike in traffic can help you take preemptive measures before AuthBots cause any damage.
3. Build Capabilities to Identify Automated Activity in Seemingly Legitimate User Behaviors
AuthBots simulate mouse movements, perform random clicks, and navigate pages in a human-like manner. Preventing such attacks require deep behavioral models, device/browser fingerprinting, and closed-loop feedback systems to ensure that you don’t block genuine users.
Purpose-built bot mitigation solutions detect such sophisticated automated activities and help taking preemptive actions. In comparison, traditional security solutions—such as firewalls and WAFs [web application firewalls]—are limited to tracking spoofed cookies, user agents, and IP reputation.
Also, building or deploying a dedicated bot-management solution will not only allow you to restrict AuthBots on login pages but can also help in eliminating other types of automated attacks that are performed after login, such as web scraping, checkout abuse and denial of inventory.
Radware Ltd. is a provider of cybersecurity and application delivery services.
Favorite